Remote Browser Isolation (RBI): The Definitive Guide to Modern Web Security
In an era where 90% of enterprise work happens within the browser, the web has become the primary battlefield for cyber threats. Traditional security measures like antivirus software or firewalls are no longer sufficient against sophisticated Zero-day exploits or highly targeted phishing attacks. This is where Remote Browser Isolation (RBI) changes the game.
What is Remote Browser Isolation (RBI)?
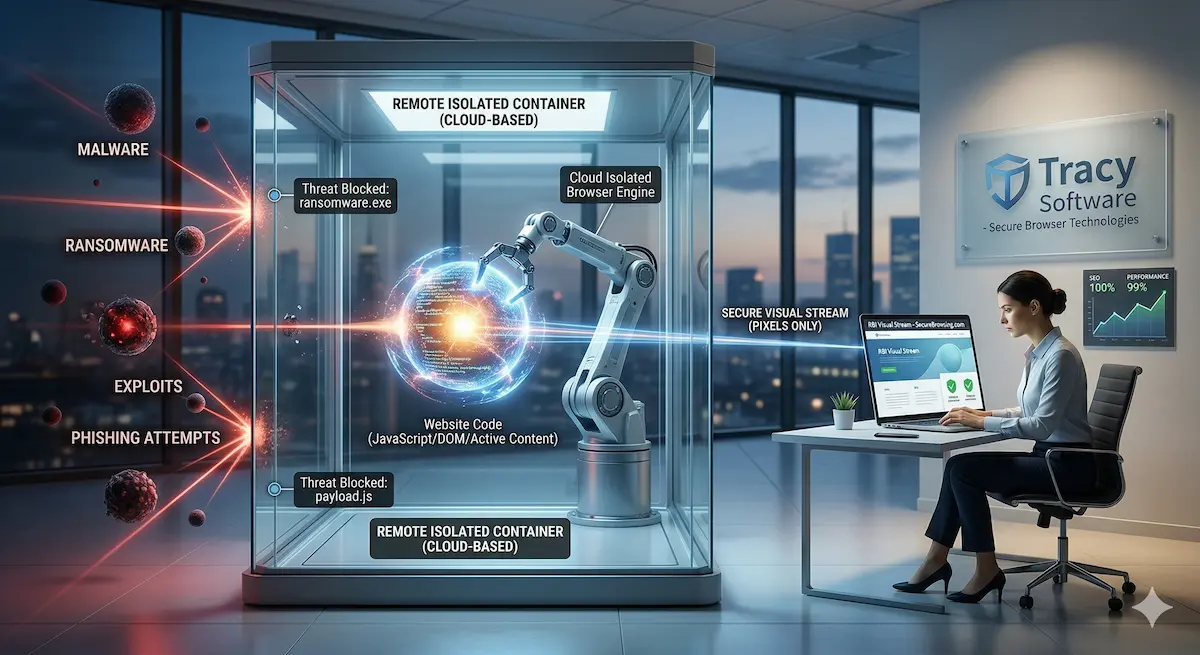
Remote Browser Isolation operates on a Zero Trust principle. Instead of trying to "guess" whether a website is safe (detection-based security), RBI assumes every site is potentially hostile. When a user browses the web, the browser doesn't actually run on their local machine. Instead, it runs inside a disposable, isolated container on a remote server in the cloud.
The user receives only a secure visual stream of the website, while all active code — JavaScript, CSS, and HTML — remains miles away from the corporate network.
Think of it this way: It's like handling hazardous materials through a lead-shielded window using robotic arms. You see everything, you perform the task, but the danger never touches you.
Why Organizations are Switching to RBI Technology
1. Total Elimination of Malware and Ransomware
Most malware enters an organization through "drive-by downloads" during routine browsing. With RBI, because the code never reaches the endpoint, the malware is trapped in the remote server and is instantly destroyed the moment the user closes the tab.
2. Neutralizing Phishing Attacks
Advanced RBI systems can render suspicious pages in "read-only" mode. The user can see the site, but the system prevents them from entering credentials or sensitive data — neutralizing the phishing attempt before it can even happen.
3. Seamless User Experience (UX) without Compromise
In the past, organizations would block half the internet to stay safe. RBI allows employees to browse freely and safely, even on uncategorized sites, without taxing their local hardware. Since the heavy lifting happens in the cloud, the user enjoys a fast, lightweight browsing experience.
4. Application Isolation for Internal Tools
Enterprises also use RBI to protect their own internal web applications. By exposing the app only through an isolated browser, the organization ensures that sensitive data is never stored in the local machine's cache and cannot be illegally downloaded.
Our Expertise in Browser Engines and Chrome Automation
Developing a robust RBI system requires a deep understanding of Chrome automation and the inner workings of browser engines. The ability to "deconstruct" a webpage and reconstruct it securely is at the core of what we do.
At Tracy Software, our background in developing browser isolation solutions allows us to offer more powerful, faster, and more secure browser automation tools. We don't just automate the browser — we understand its architecture at the most fundamental level.